IoT communication monitoring solution
Monitoring Challenges in the Internet of Things
With the rapid development of Internet of Things (IoT) technology, billions of IoT devices are widely used in smart cities, industrial automation, smart healthcare, smart homes, and even AI agents. This has made IoT monitoring and security management a common and necessary infrastructure across these scenarios. However, the successful experiences from IT system management are difficult to replicate for IoT devices. This is due to several reasons:
- IoT Devices are Mostly Closed Systems: Even if their core is based on Linux/Windows, they cannot install log agents or EDR (Endpoint Detection and Response) systems like IT devices to obtain more device information.
- Limited Monitoring Capabilities of IoT Devices: Most internal system information of IoT devices is not accessible externally, with only a small portion of data being sent out via SNMP or logs.
- Diverse Communication Protocols and Application Scenarios: IoT devices often utilize various communication access technologies such as Ethernet, Wi-Fi, 5G, and 4G, which increases the overall complexity of the application system and makes monitoring more difficult. For example, a robot (IoT endpoint device) connected to a 5G router (IoT network device) may have its network connections unidentifiable due to the NAT mechanism of the 5G router.
- Advanced application scenarios require IoT big data: By observing the interactions between IoT devices and external entities (such as communication behavior and even communication content), the obtained raw data is organized into metadata, serving as the foundation for big data analysis.
Since directly monitoring IoT devices is challenging, monitoring the communication behavior of IoT devices becomes critical. Through IoT communication monitoring, we can:
- Instantly grasp device operational status (whether it is functioning normally or exhibiting abnormal behavior).
- Analyze cybersecurity risks of IoT devices (such as detecting abnormal access or malicious communications).
- Support AI big data analysis and digital twin systems (mass data collection, correlation, and filtering).
PacketX IoT Communication Monitoring Solution: NPB and Metadata Analyzer
PacketX's IoT monitoring solution is designed based on the principle of non-intrusive deployment and includes the advanced NPB and Metadata Analyzer.
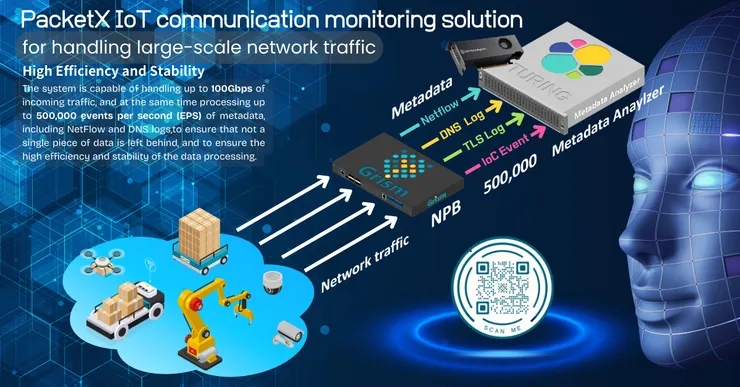
PacketX IoT Communication Monitoring Solution: NPB and Metadata Analyzer
GRISM Network Packet Broker (NPB)
PacketX's GRISM NPB can be used to tap into IoT network traffic and perform immediate IoC (Indicators of Compromise) matching and metadata extraction to ensure the visibility and security of IoT communications.
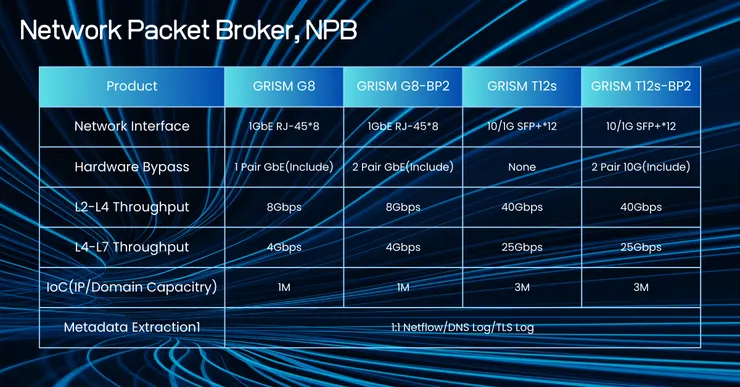
Network Packet Broker, NPB
Its main functions include:
- Traffic Tapping and IoC Matching:
GRISM can use Sniffer mode to tap IoT network traffic and compare it with a periodically updated IoC database to detect potential malicious behavior, while simultaneously sending IoC match events. - Metadata Extraction and Event Logging:
Extract metadata from IoT network traffic, such as NetFlow, DNS logs, RADIUS logs, and TLS logs to capture critical communication behaviors. - Integration with Third-Party Security Devices:
Based on security policies, specific traffic can be filtered and directed to IDS/NDR (Intrusion Detection System/Network Detection and Response) security devices to enhance overall protection capabilities.
TURING Metadata Analyzer
TURING is a high-performance event collection and correlation system launched by PacketX, built on ELK, specifically designed for handling IoT network operations and security event analysis.
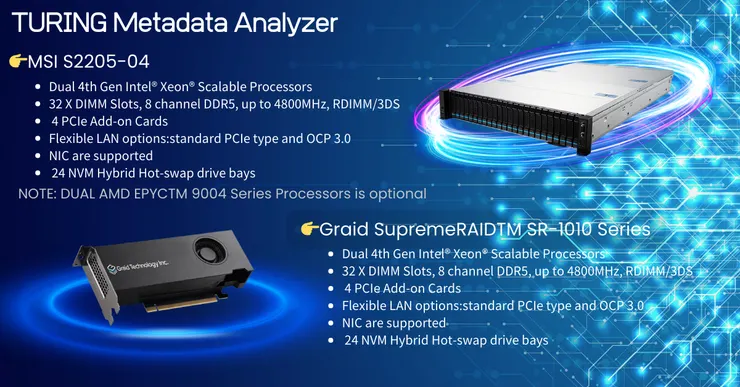
TURING Metadata Analyzer
Its main functions include:
- IoT Event Correlation Analysis:
🔘Receives metadata and IoC match event logs from GRISM.
🔘Combines IoT communication metadata with IoT device logs to
construct a complete context for IoT events.
🔘Conducts anomaly detection and risk assessment. - Large-Scale Event Processing:
In the era of the Internet of Everything, the volume of IoT events is enormous. TURING utilizes x86 servers paired with GRAID ultra-high-speed RAID cards, providing a processing capability of 500,000 EPS (Events Per Second) to meet the massive I/O demands of data import and real-time analysis.
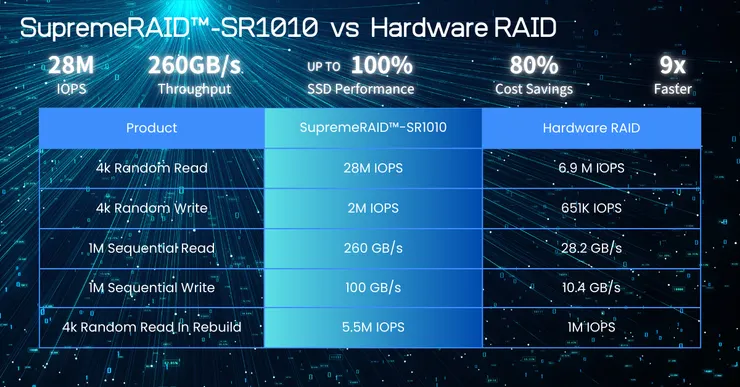
SupremeRAID™️-SR1010 vs Hardware RAID
New Perspectives in the New Era of the Internet of Things
In a complex application system that extensively utilizes IoT devices with various access technologies like Ethernet/Wi-Fi/4G/5G, the success or failure of IoT monitoring is crucial to the stability and security of the entire application system. In response to the aforementioned challenges, PacketX integrates network traffic tapping analysis, IoT communication devices, and hardware-accelerated databases to develop next-generation IoT monitoring systems. This will serve as a key driver for continuously optimizing the resilience and performance of advanced applications such as smart cities, smart manufacturing, and AI agents.